You are hereProducts / Chroot for Windows
Chroot for Windows
Download Now
Introduction
Chroot is a popular Linux tool that allows you to run a program that cannot access files outside of a specific file system folder tree. Now, using undocumented features, a native Windows version is available that doesn't require the usage of Cygwin or any additional software.
Due to the differences in operating system between Windows and Linux, this version provides a bit more flexibility that that provided and indeed required by the original. For one, you can choose how severely to chroot a program, preferring to blocking off access to one, a few or all of the available drives present in your computer configuration.
Version 2.0 also allows redirection of registry accesses, to further jail and isolate the process.
Please note, as it does use undocumented parts and features of Windows that Microsoft may change without warning in any update, using it for any mission critical situatons or as a replacement for true sandboxing tools is not recommended.
Usage
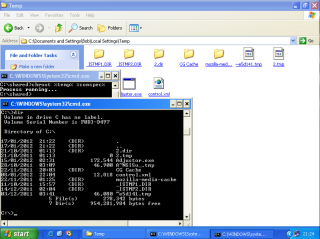
Usage: chroot rootDir [options] program args
Where [options] can be none, one, or more of these:
-h Shows this help
-v Shows the version banner
-a Run 'program' as an anonymous user
-u
-f
-r
-rl
descendents
-rp Persist created registry keys across reboots
Note -a and -u cannot both be defined. If neither is defined
'program' will be run as the user running chroot
e.g. to allow 'program' to access drives C: and D: as normal
the format of the option would be -f cd
In registry redirection:
-r
equivalent to -rlm
-rcr
When the -rf option is specified, keys for the 4 branches (Machine, Users,
ClassesRoot and CurrentUser) are created automatically under the specified
path. By default these keys exist only until you reboot the computer.
To make them persistent across reboots, use the -rp flag
Valid registry path prefixes are HKLM for Local Machine, HKU for Users
HKCU for Current_User and HKCR for Classes_Root. Example registry options:
-r HKLM\\Software\\Jail
-rcu HKCU\CurrentUserRoot
-rcr HKCR\\SecondaryRoot
'rootDir' and 'program' can contain environment variables.
Limitations
Since any process can chroot any other it has access to without any special privileges, there's no ultimate guarantee that a rooted process will stay rooted. While that is true, it is by no means a common occurance.
Unlike the Windows default of un-chrooting children of rooted processes, Chroot 2.0 now ensures that children don't break free. This is a change from version 1 which left children to their own devices.
A third limitation is that, unlike Linux, you can't use this tool to create a second 'version' of Windows in the new root directory. This is due the effects of both a) KnownDLL loading, which overrides the jail b) the volatile, numbered nature by which system calls are made.
Because of the way processes start under Windows, it is impossible to redirect all registry accesses until after a certain point. This applies mainly to OS components such as ntdll and kernel32 but extends to the DllMain's (startup code) of all statically linked dlls. Any accesses made after this (including usage of keys opened before) are trapped.
Without the correct entries in the new location, redirecting HKEY_LOCAL_MACHINE will lead to failures in some API's which use the registry to find dll paths, this is mainly a problem for tools that work with DACL's using the advapi32 security API.
How it Works
The tool works by running and pausing the requested program, changing what it sees as the location of the file system drives, and then letting it go on its way. This is achieved via the use of device maps, there is a more in-depth technical blog posting on the process and how it works here. Registry redirection is achieved by hooking and providing modified versions of the system registry functions.
Download
The download includes both x86 and x64 binaries. 7-zip is required to unpack the download.
Download Now
Size: 255 KB
MD5: 608ce7041ddab522f137e880c1bdeeed
SHA256: a70da8af68b6bf32c7d2c1448c86cb3f3b6437e6e551991cf9d912a528bf38a7